Ngharo got this started with going around the room and asking everyone what they have been hacking and what they plan on hacking on next, then talking about some improvements to the dc414 server, such as how it is now fully IPv6 friendly and some improvements to the VPN. Then I gave a demo of how BeEF when used with Metasploit can pwn browsers from the inside out. dw5304 stepped in and showed us how to use the windows 7 UI on windows 8 with out having to worry about updates messing things up. Then Noize stepped up and gave us all a great introduction to Subterfuge, a MITM framework that utilizes arp attacks. Then I attempted to give another demo but failed, more on that later 😉 We spent the rest of the night drinking, eating cupcakes “thanx darkwinds wife” and loling at horror pics of server rooms and wiring closets. Congrats to Castor, Tony, and Peppergomez for winning the dc414 free junk giveaway!! Enjoy your junk guys 😛
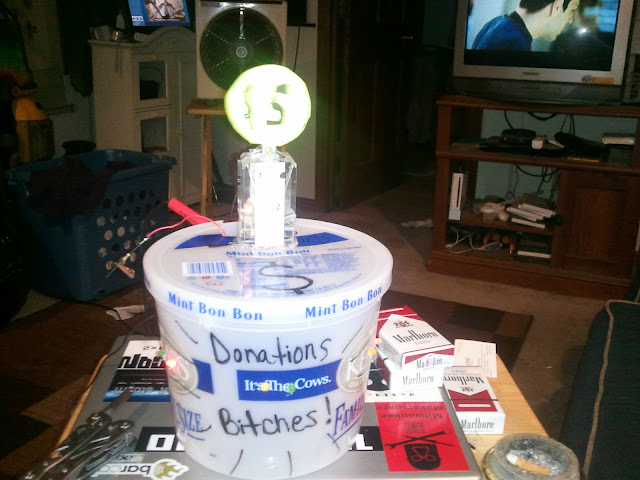
We got $42 in donations which paid for the pizza and some of the beer with nothing left over for the server :/ which cost about $71 a month. Remember your donations are what keeps dc414 running smoothly for YOU!!!!